I’m reluctant to write this up. I feel I’m wandering onto really fresh turf here. Because this is really about style and design; and the various audiences that craft addresses. Something I don’t really know anything about.
One thing that caught my fancy in the book “Buying In” was the idea that products are two faced, like the middleman. Products you use in public, like an iPod, have one face they show to the public and another which they show to you. To hear him tell it when the iPod first appeared cultural observers took two quite polar positions about it. Some celebrated way it empowered a deeper intimate relationship between citizens and their music collections. While some railed about how the white headphones created a tribe, a kind of social signaling, and members of this tribe were walling themselves off inside a cult of iPod.
There is a large literature that presumes most style and fashion exists to serve a social signaling function. For example to denote membership in a tribe or to make the owner appear high-value. And no doubt that is one function of style, but yet I’m starting to think such talk is often just a cheap shot. It’s easy to see the signaling, the public face of the product. It’s hard to see the private face. Intimate relationship between the user and the product and intimate and complex relationship between the member and his tribe.
There are some products were this public/private tension is particularly high. I have a beautiful scarf. Nice enough that people feel free to comment on it. But they have no idea how sensual it’s cashmere is, nor other things about it I’ll pass over.
In another portion of the book he mentions how some publishers engage claques to ride public transportation reading new books, carefully so other passengers can take note of their dust jackets. In telling the iPod story it sounds as if Apple’s designers were largely unaware how the white headphones would create a unified field for the products branding. That white headphone decision appears to have been forced by the white packaging. Of course Apple is often quite aggressive in shaping the public face of their products. The iPod on the table here is black, but the headphones are still white.
The public/private face of stuff takes a odd turn when you move into a private space, say someone’s home or office. Corporate buyers sometimes decorate their offices with false signals to undermine the salesmen, i.e. photos suggesting hobbies the buyer doesn’t actually engage in. I once scanned the book shelf at a party only to become confused by the diversity of the owner’s taste. Later I discovered the owner was a publisher and he had a copy of most everything the firm had ever published.
I have gone into homes that are indistinguishable from a high end hotel suite. I wonder then, does this mean the owners have no intimate relationships with stuff; or does it mean they are just that aggressive about keeping that information private. I’ve been in the homes of some people so rich that they have rooms which reveal only a public self, while further in you’d find more revealing rooms. People do manage their public presentation of self, and if you often bring people into your private home then your likely to manage it there.
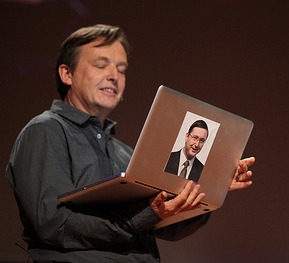
Yesterday Karim came at this from another side, writing on “The Anti-Social Nature of the Kindle.” He complains about how his Kindle denies him the ability to present a public face. But I notice how Amazon, the middleman, stripped one of the product’s two faces of as it passed thru their distribution channel. And while that must drive the publisher’s crazy, as Karim points out sometimes you want to reveal the public face of your stuff.
 Lauren Weinstein
Lauren Weinstein