Some more about this book, Democracy for Realists: …
If we accept that voters do not vote for their policy preferences (and you can read the book if you want to see the evidence) then what is driving their voting behavior.
Here are two models that Political Scientists have put forward – space and time. Both model presume that voters, being humans, lack the time or talent to engage in a very subtle or complex analysis of what to do with their vote; so they simplify things. They approximate.
The spacial model: all of politics is boiled down to some simple metric: left-wing v.s. right-wing say. Or maybe a few two, like both an economic and social variant of left/right. The voter then “merely” asks the question how close are these candidates’ metrics to my personal metrics. He then votes for the one closest to him.
In the time based model the voter need only look at his personal experience over time. He then aligns that with who ever is change during various time frames and votes for the candidates that deliver better outcomes. It’s feedback loop, and presumably the statistics of large numbers of voters might make this work out nicely.
Again this is Science. A theory is only interesting if we can proceed to try and disprove it.
The spacial theory is easy to disprove. You just ask. Compare the voter and the candidate he selects on the metric. Questionnaires can dependably tease out where they are on the scales. For example: Support for lower taxes verse more government services? What the data shows is only the lightest correlation. In fact in some cases voters do the opposite of what they prefer. So this theory isn’t helping us.
The problem with the time based theory is two fold.
The first problem: The usual ones found in feedback based systems. These systems only work if (a) the signal the feedback is based on is accurate and (b) the feedback’s timing is adjusted correctly. In Engineering school I spent a few years learning how to get that right for simple electronic systems like amplifiers. In that context if you get it wrong you get nothing or horrific feedback noise. Big social systems are even harder. So first off voters get a signal (they lose their job, the weather is lousy, the crop fails, the town has an awesome fair, the kid gets a lovely teacher) and they sum that up and vote for against the current candidate. Then we have timing. This model rewards the politicians for taking actions that have short term benefits; i.e. they show up in the voter’s impression before the next election. Worse, long term benefits will accrue to the account of some other guy.
Like the spacial model voters have a very noisy model of the candidates. In this case the their model of credit/blame is very poor.
So what are two models worth anything? Turns out yes.
The spacial model is the gold standard for understanding legislatures. While it’s useless for discovering how a voter will pick his candidate, it useful for predicting how Bob, your legislator, will choose to vote on any given bill. This is good news: Bob is fairly well informed about the position taken by the bill. On the other the voters who elected Bob do not have a good model of Bob.
The time based model is actually quite predictive of how voters will behave. But, oh my, they are largely miss informed about blame/credit and their sample is narrow minded. They only look back a few months. This is not good if you want responsive government. It is useful if your placing bets on an election. You can do a damn good job of predicting the outcome of elections by measuring just GDP growth over the last few months.
While these models are not as useless as the folklore model ( i.e. that voters give their votes to candidates who reflect their personal policy preferences). But if your goal is to explain how Democratic governance is responsive to the voters preferences; they they aren’t going to help you.
More to follow…
 Yet another attempt to create a social network. This one’s called Mastodon. It is analogous to Twitter, i.e. short status updates with following, liking, comments. Web UI, and apps for assorted devices. It’s usenet like in with a user accounts residing on nodes and then the nodes stitched together into an exchange network. Open source with ties to the FSF/Gnu community.
Yet another attempt to create a social network. This one’s called Mastodon. It is analogous to Twitter, i.e. short status updates with following, liking, comments. Web UI, and apps for assorted devices. It’s usenet like in with a user accounts residing on nodes and then the nodes stitched together into an exchange network. Open source with ties to the FSF/Gnu community.

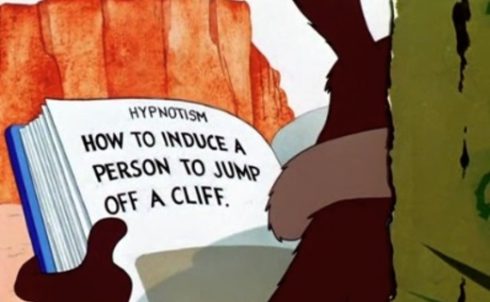 You may have noticed that sometimes: you argue with somebody and you come away thinking: “My that backfired!” Rather than loosening their attachment to their foolish belief they have become more committed.
You may have noticed that sometimes: you argue with somebody and you come away thinking: “My that backfired!” Rather than loosening their attachment to their foolish belief they have become more committed.